Insufficient Authorization Vulnerability in Yahoo! Pipes
Recently, I found an interesting issue qualifying on Yahoo! Pipes. But before going into the details of this specific issue, let’s understand some basic points.
What does Authorization mean? In general, authorization relates to the set of activities which a user can perform once logged on to a particular system. This is typically divided into the following two categories:
- Horizontal Privilege – Basically all user having same the same rights – for example, all Facebook users
- Vertical Privilege – User having different access rights – such as an Admin user and a Normal User on a particular application.
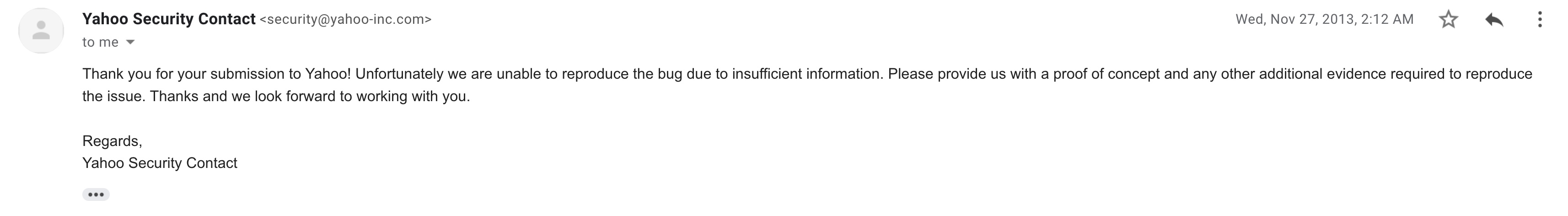
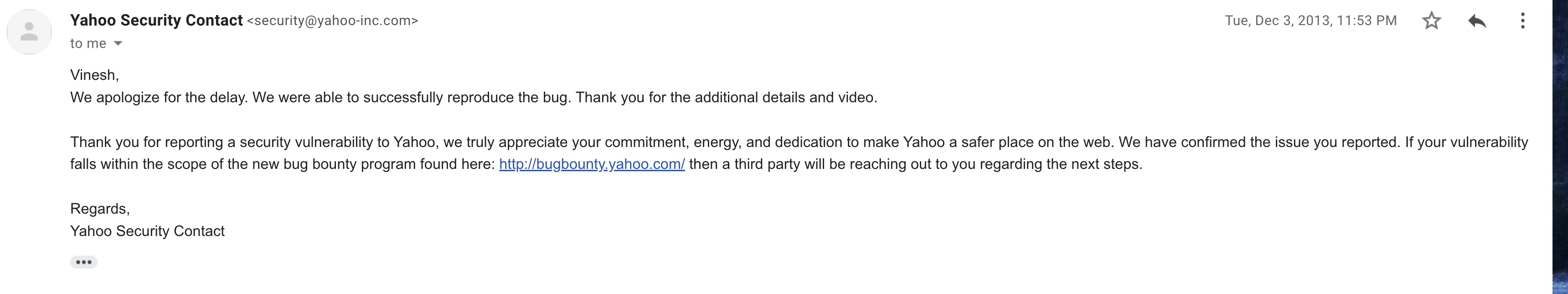
The issue I found on Yahoo! relates to improper implementation of CSRF token validation, where the CSRF token generated by an attacker can be used to change the environment of victim. The Yahoo! Security team informed me that the issue was successfully reproduced once but then later they just couldn’t reproduce it again. They fixed this issue but did not reward me with a bounty. But never-mind I found this issue pretty interesting so here are the details on it:
Issue was reported on 12 Nov 2013 to Yahoo Security Team. Vulnerable Website: http://pipes.yahoo.com
Impact: Attacker can publish and unpublished pipe created by a victim using attacker CSRF token. Also there was no authorization in place.
Here are the steps for this attack:
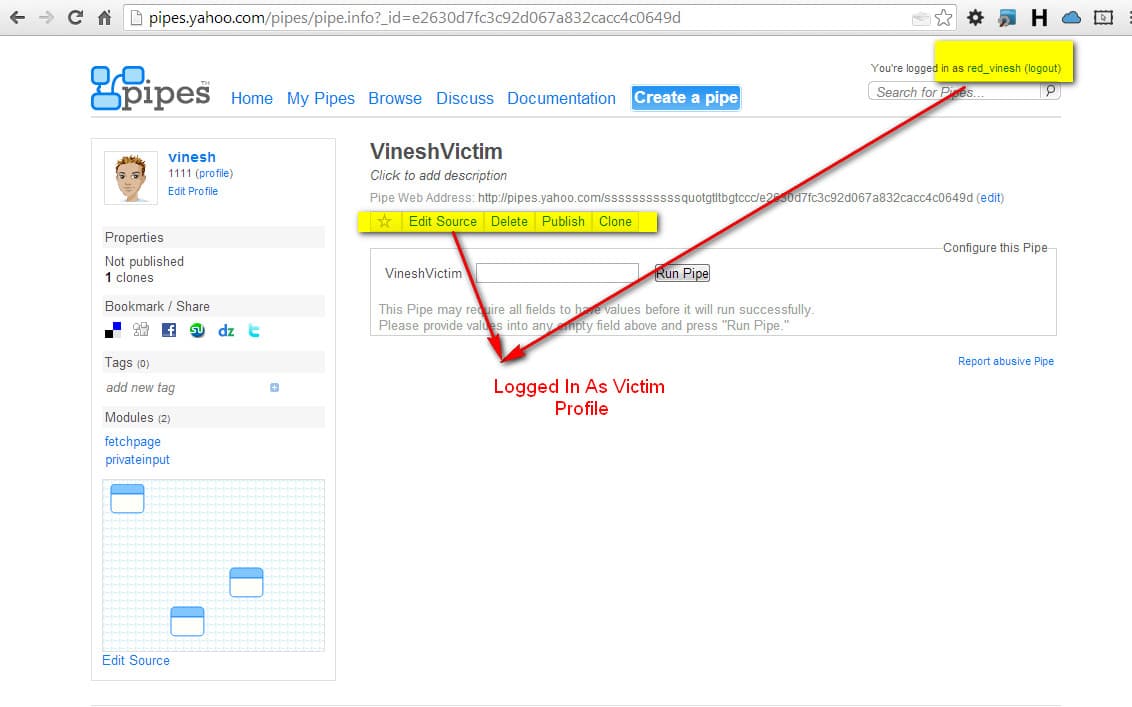
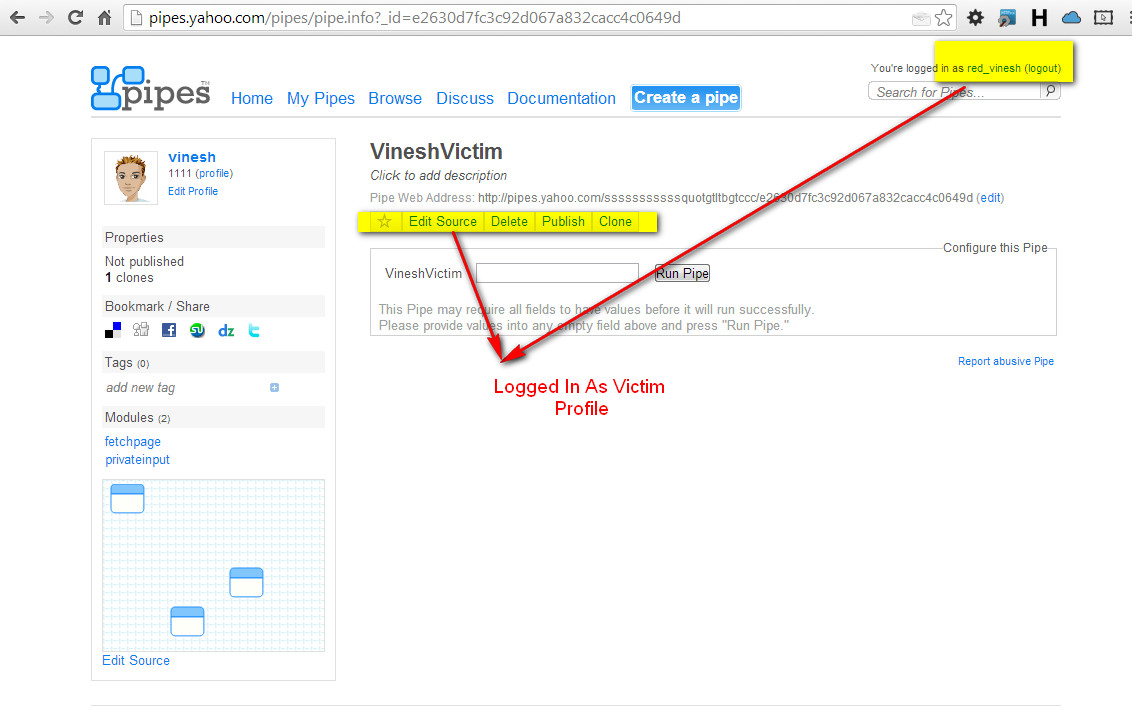
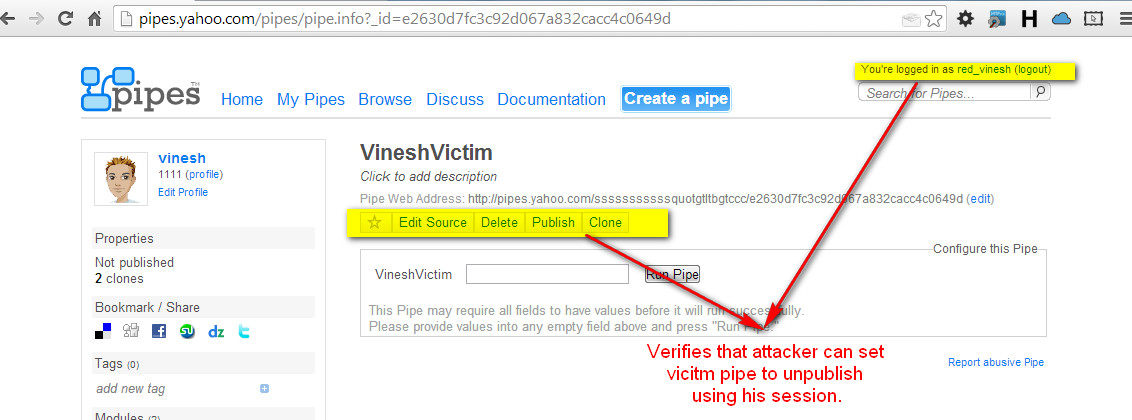
- Step 1: Logged in with the attacker’s credentials.
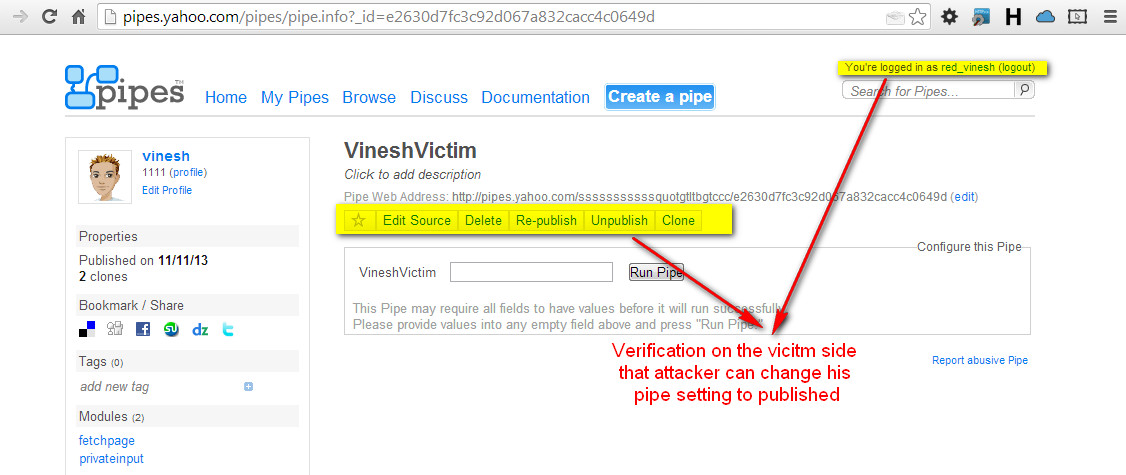
- Step 2: Then search for any pipe you want published. Here I used my pipe which was created with another account, which we shall call the victim account. htttp://pipes.yahoo.com/pipes/pipe.info?_id=e2630d7fc3c92d067a832cacc4c0649d
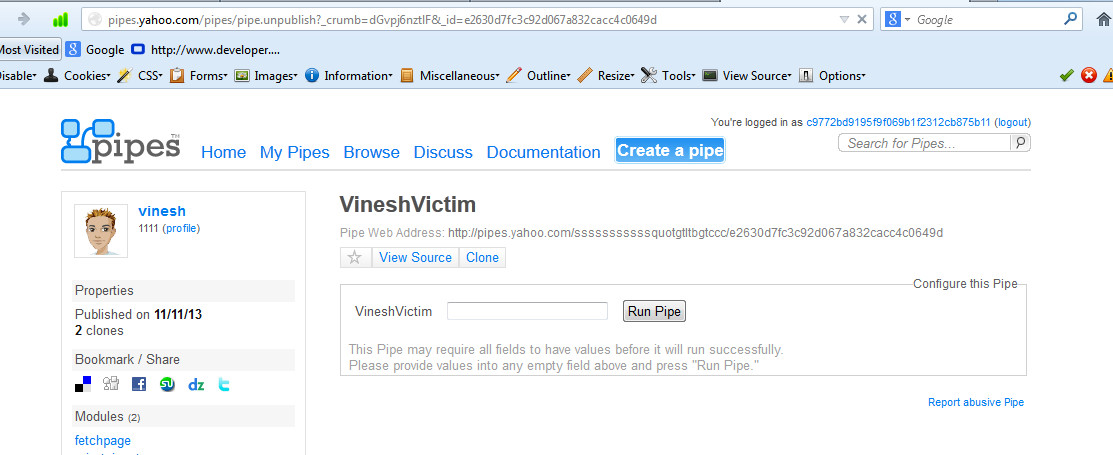
- Step 3: You can see the in the Properties of this Pipe that it was Not published (see left hand side corner).
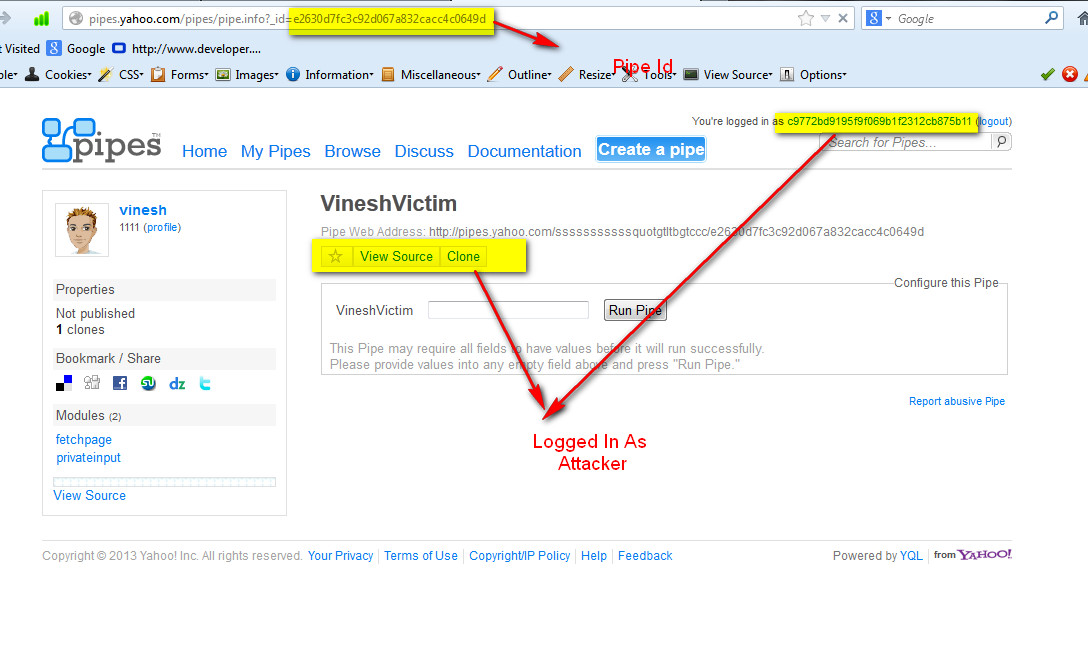
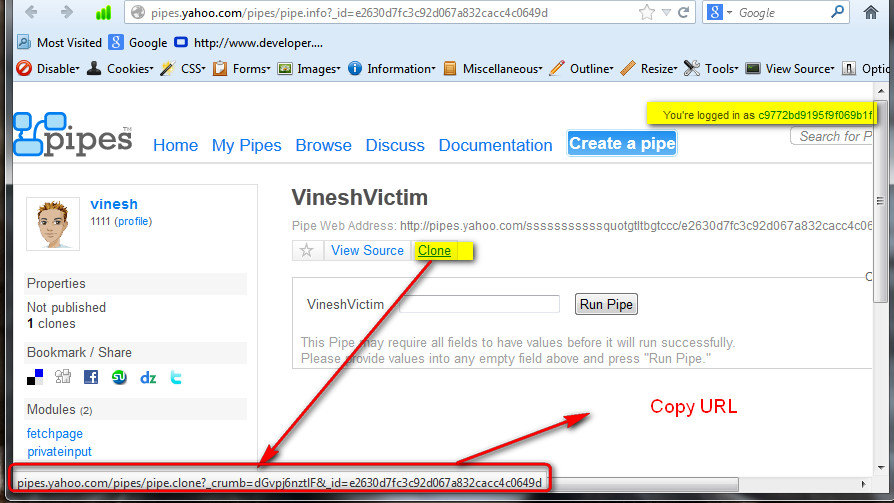
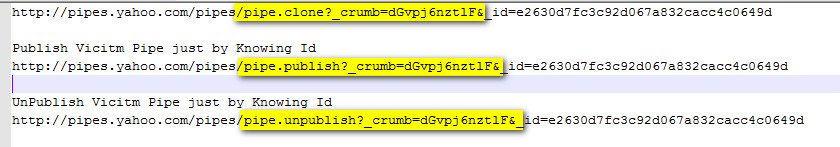
- Step 4: Right-click on clone and copy link address as shown in the above URL
- http://pipes.yahoo.com/pipes/pipe.clone?_crumb=43QDHVwUial&_id=e2630d7fc3c92d067a832cacc4c0649d
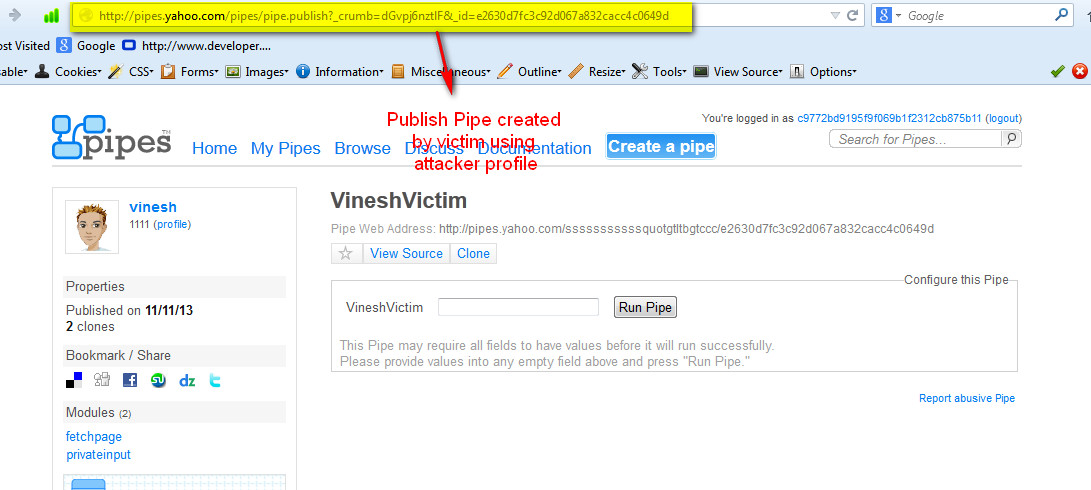
- Now change pipe.clone to pipe.publish to publish this pipe. http://pipes.yahoo.com/pipes/pipe.publish?_crumb=43QDHVwUial&_id=e2630d7fc3c92d067a832cacc4c0649d
- Step 5: The pipe is now successfully published.You can verify from the Properties of the Pipe that it was published (again, see left hand side corner). Same goes for the action to un-publish a pipe. Yahoo confirmed my issue on 4 Dec 2013
below is the screenshot for the same:
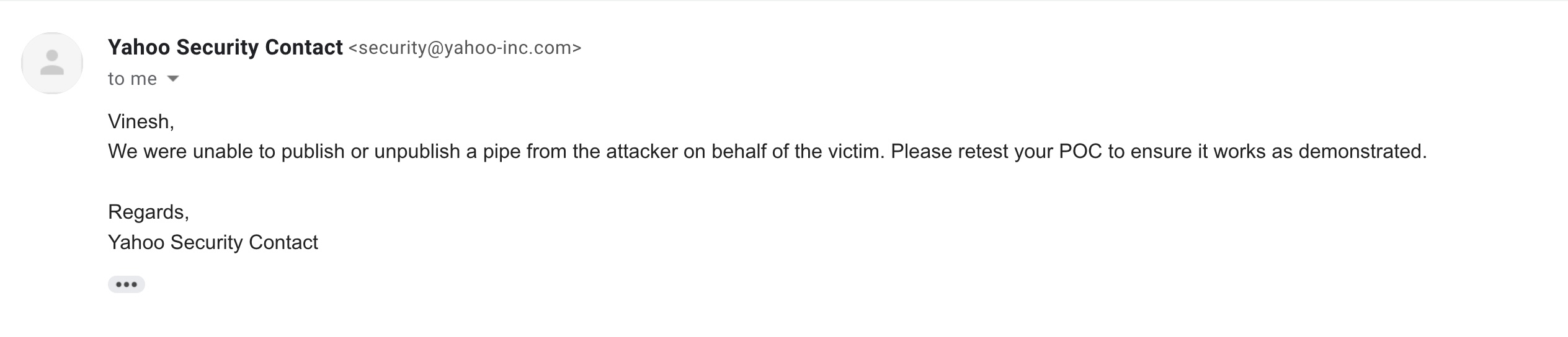
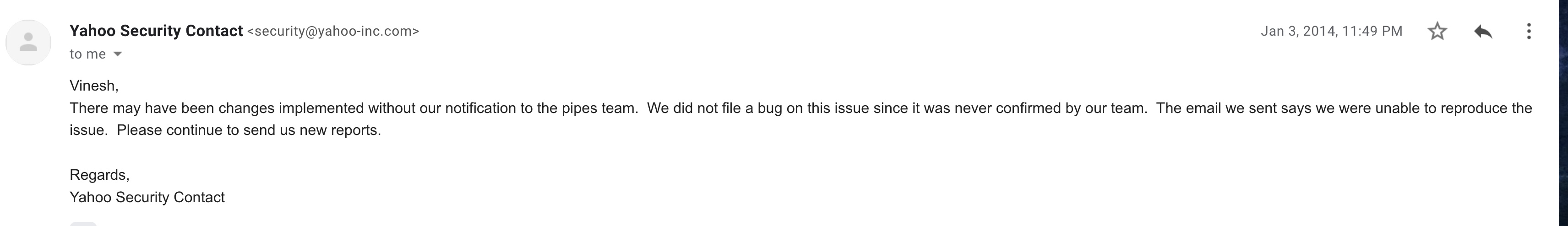
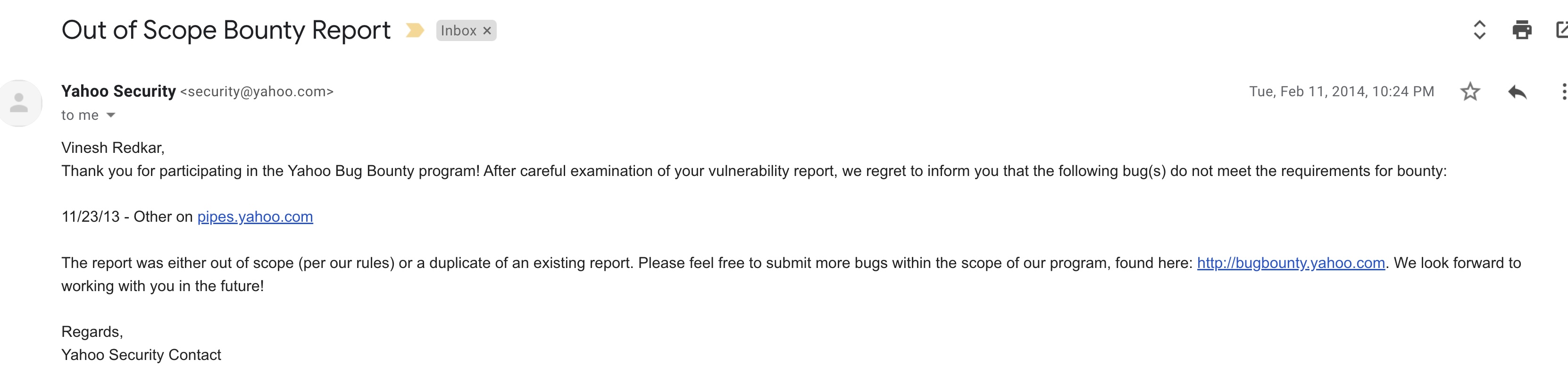
After fixing the issue, they replied saying they never confirmed issue. Following is the screenshot of reply:
 Well what can I say?
Well what can I say?
Have a look a POC video below: https://www.youtube.com/watch?v=0V8CLfyW4TE